Supported Hypervisors and Containers List
This page is for Device42 administrators who need to confirm which hypervisors and container platforms are supported for autodiscovery. Find the supported platforms below, including details and limitations for Docker, Cisco ASA/NX OS, and Nutanix autodiscovery processes.
If you are looking for instructions to get started with Hypervisor, Linux (*nix), or Windows discovery, see the Windows / Hyper-V Discovery page or the Linux / UNIX server auto-discovery page.
Supported Hypervisor and Container Platforms
Device42 is constantly expanding the hypervisor and container platforms supported by autodiscovery.
The list of supported platforms currently includes:
- *nix
- AIX HMC
- Cisco ASA/NX-OS
- Citrix XenServer
- Docker
- Docker API
- HPE OneView
- HPE Simplivity
- IBM i/AS400
- IBM z/OS
- KVM/libvirt
- LXC
- Nutanix Acropolis
- Nutanix Prism (v2.0/v1)
- Nutanix Prism Central (v3)
- OpenVZ
- Oracle VM
- oVirt/Redhat
- VMware
- Windows
- WinRM
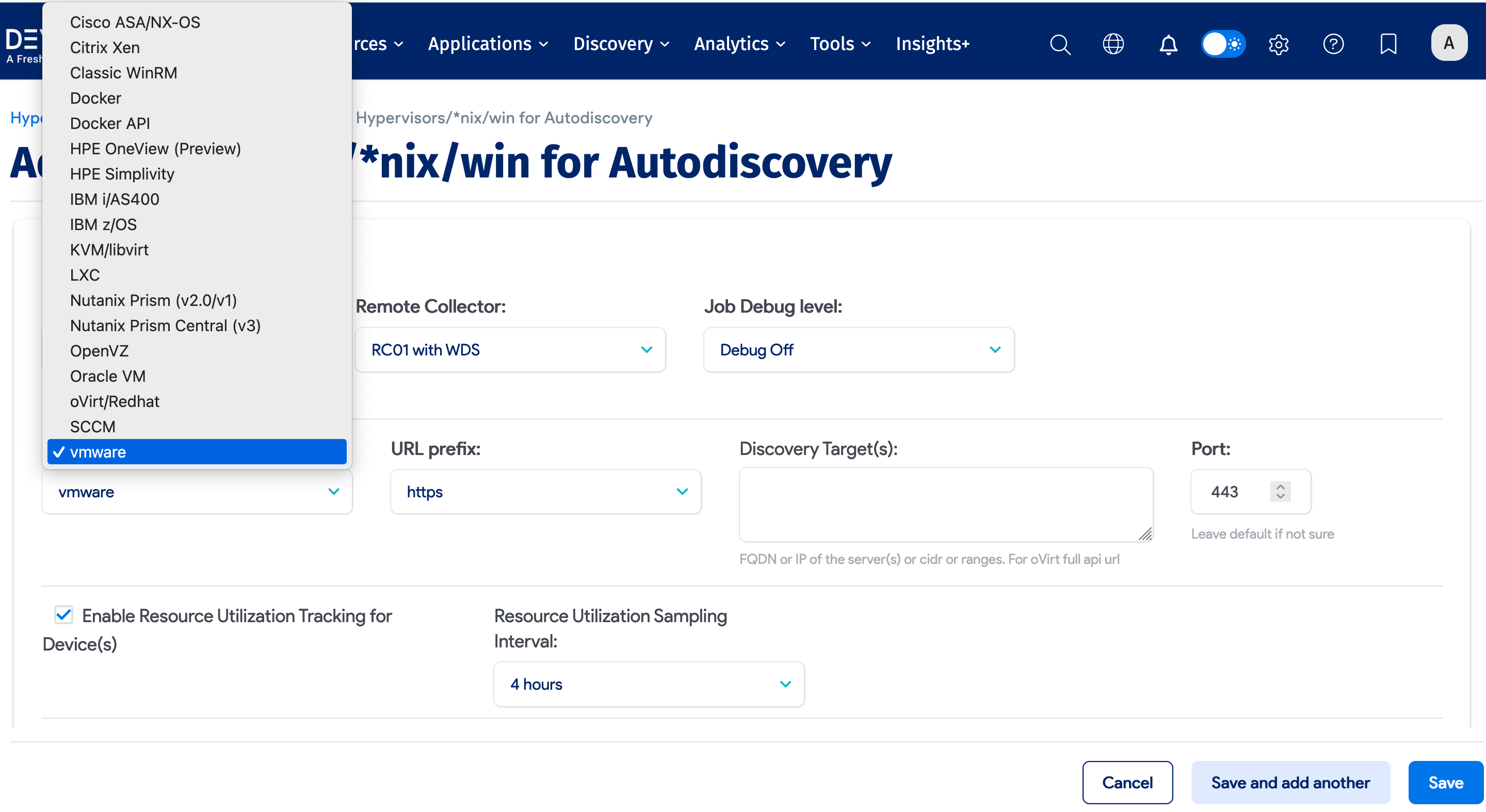
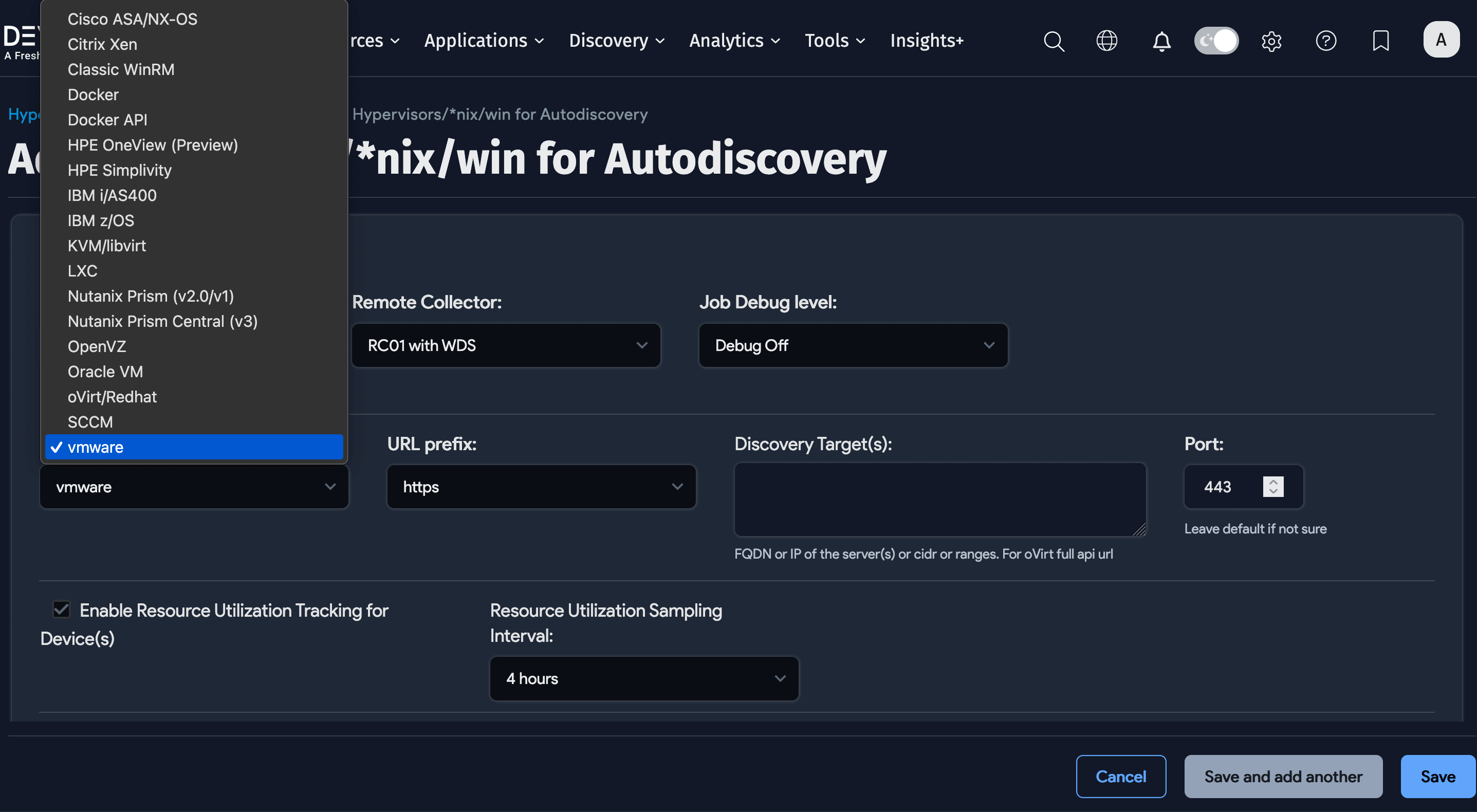
Both Windows and *nix (Linux/UNIX) can be found in this dropdown menu as well. Use those options to discover Windows servers, Linux servers, guest instances, or VMs themselves, as opposed to their hosts.
For instructions on how to configure and run these discovery jobs, see Hypervisor Autodiscovery.
If you are using a hypervisor, a container platform, or an orchestration tool you would like to see supported - please let us know! Open a support ticket or email support@device42.com.
Docker and Docker API Autodiscovery Notes
Device42 provides two Docker discovery methods: Docker API discovery returns basic container data with IPs and MAC addresses, while regular Docker discovery also returns service ports.
Device42 supports all standard Docker cloud operating systems such as EKS (AWS Kubernetes), GKE (Google Kubernetes), AKS (Azure Kubernetes), and standalone Kubernetes, as well as Ubuntu, CentOS, Debian, Arch Linux, and Fedora.
By running Docker and connecting to the host, you can map connections to the container. You can see on the Docker host how to get the source ports of containers, without having to log in to the container to identify the connection. Use the docker top command and supply just the container ID (requires sudo commands).
Cisco ASA/NX OS Autodiscovery Notes
Device42's Cisco ASA/NX OS autodiscovery augments firewall/ASA discoveries with information gathered via SSH. If you run virtual firewall instances, Device42 will discover your virtual firewalls and list them as firewall “contexts” underneath the parent firewall. Note that this discovery method has had only limited testing.
Nutanix Autodiscovery Notes
If you have previously run a Device42 discovery job and are discovering new resources, you may need to delete and re-run the job to have a complete view in some cases.
Ignore IP and MAC Addresses From Autodiscovery
You have the option to ignore specific IP and MAC addresses globally and for specific jobs. See Windows and Hyper-V Autodiscovery for more details.